In a landscape where cyber threats evolve constantly, companies face a critical decision: how to structure their penetration tests (pentest) to maximize protection of their digital assets. BrownPipe Consultoria, a cybersecurity firm with over 13 years of experience, presents an analysis of two approaches that are gaining ground in the market.
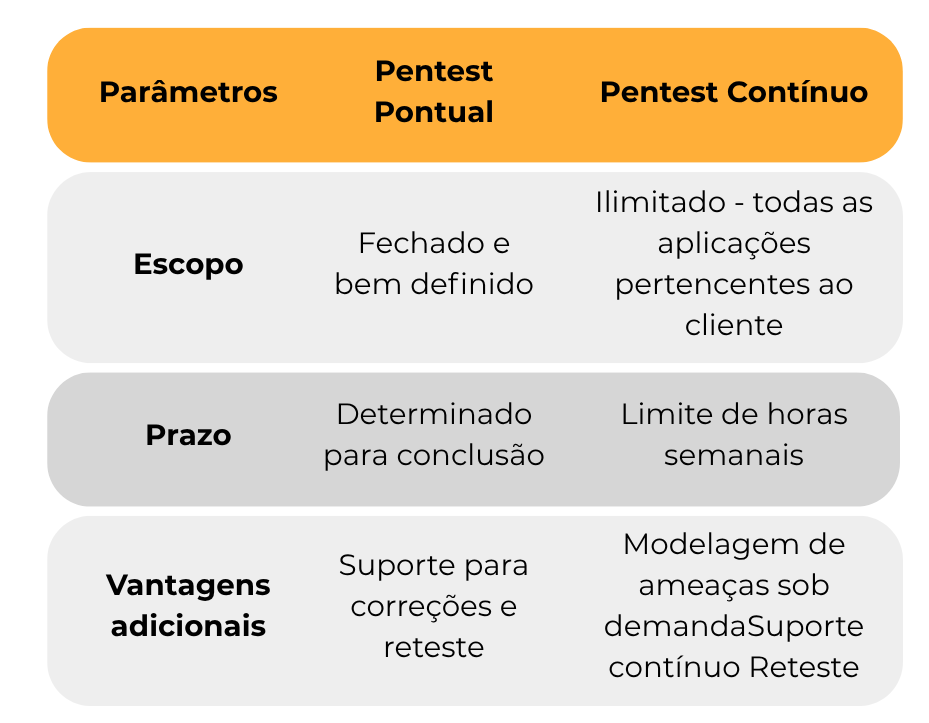
Penetration tests — essential for identifying vulnerabilities before they become security incidents — can be structured in two main ways, each addressing specific organizational needs, as outlined in the table below.
Comparison Between Modalities
The Point-in-Time Pentest involves testing a specific set of applications within a clearly defined scope and timeframe. This modality serves companies that need focused assessments of critical systems or systems that have undergone significant updates.
The Continuous Pentest, on the other hand, offers a more comprehensive approach, enabling regular assessments across the organization's entire application portfolio. The flexibility to prioritize targets makes this modality particularly attractive for growing companies or those in active development of new systems.
BrownPipe's Differentiator
Regardless of the modality chosen, the BrownPipe team provides ongoing support to guide clients in remediating identified vulnerabilities, including verification of remediation effectiveness through retesting.
BrownPipe also offers a distinctive pentest approach: unlike many market solutions that rely solely on automated testing, BrownPipe focuses on thorough manual testing to uncover flaws that automated tools miss.
Threat Modeling: The Continuous Modality's Edge
A key distinguishing feature of the Continuous Pentest is the inclusion of on-demand threat modeling activities. This service allows organizations to receive proactive guidance during the development of new systems — identifying potential security risks as early as the design phase.
Threat modeling integrated into continuous pentest represents a paradigm shift: from reactive security to security by design.
Decision Criteria
The choice between modalities should take into account factors such as IT infrastructure maturity, frequency of new application releases, available resources, and corporate security strategy. Companies with stable environments may benefit from the point-in-time model, while organizations with continuous development cycles tend to get greater value from the continuous model.
Need guidance on which modality to choose?
Our team of experts is ready to analyze your specific scenario and recommend the most appropriate strategy.